5 Cybersecurity Lessons From the Ukraine War
- Mattia Campagnano
- Jun 16, 2022
- 6 min read
Updated: Nov 14, 2024
The recent developments of the situation in Ukraine has led to new threat scenarios of modern warfare, fought not only through traditional weapons but also on the information security scene, which poses an unprecedented threat to governments and organizations. According to public reports, Russia allegedly launched devastating cybersecurity attacks on critical infrastructure, such as satellite modems and energy grids.
Such attacks could lead to catastrophic consequences to the civilian population and affect the rest of the world, given the interconnected nature of today's global economy and the strategic importance of Russia's natural gas and petroleum and Ukraine's agricultural products on the world market.

CISA Shields Up Guidance
CISA (Cybersecurity and Infrastructure Security Agency) has provided some guidelines for organizations and their members to ensure a proactive approach to cybersecurity.
Organizations should:
Ensure all software is up to date to remediate potential known vulnerabilities.
Take steps to lower their reporting threshold to senior management and the U.S. government.
Prepare to defend against critical threats based on this CISA list.
Remain vigilant toward common Russian TTPs.
Employees should:
Review their personal and work logins to ensure that passwords are difficult to predict, the same password isn’t reused on multiple websites, and that multi-factor authentication is enabled when possible.
Exercise caution when clicking links, downloading files and sharing content.
Five Lessons from the Ukraine War
Best practices guidelines allow organizations to respond to five lessons learned from the Ukraine war:
Implement an effective asset inventory management program: Organizations don't often have full knowledge of all their network assets and their purposes. This creates blind spots that threat actors can leverage to go undetected, often for long periods of time. Such blind spots need to be identified and proactively removed as soon as possible. For example, if business reasons do not justify running an outdated, on-premises Exchange Server installed in 2015, and no one knew such a server was still running, it should be decommissioned and/or moved to the cloud.
Implement vulnerability management and patch management program: Organizations need to stay on top of the evolving world threat scenarios and reduce their attack surface as much as possible. It is paramount for organizations to implement their own vulnerability and patch management program and proactively remediate potential attack scenarios before threat actors could leverage them. Said program should be conducted both against the organizations' externally facing infrastructures and their internal networks. In fact, though external attackers might cause a lot of damage, the most dangerous scenario is related to insider threats, such as disgruntled employees. Internal networks are often configured less strictly than external networks, as valid credentials are required to access them. For this reason, while organizations strictly monitor external threats, they should also pay close attention to internal threat scenarios coming from insider threats, who often have valid access credentials and enough knowledge about the network structures to severely damage the organizations (especially if they're System Administrators). Keeping operating systems and other software components up to date through an efficient patch management program is paramount to preventing potential breaches. Also, a regular vulnerability management program allows the organization to define a baseline of its security posture and monitor its changes over time.
Implement network segmentation: Organizations should divide their networks into multiple segments that are easier to defend and can be isolated from the rest of the network. Segmentation works by controlling how traffic flows through the network. They could choose to stop all traffic in one part from reaching another, or they can limit the flow by traffic type, source, destination, and many other options. How organizations decide to segment their network is called a segmentation policy. A well thought out segmentation policy can dramatically improve an organization's security posture. Attackers breaching a well-hardened internal network are confined to the specific segment they infiltrated and can't move to other segments. This way attackers can't compromise vital parts of the internal network, as they can be more easily and quickly contained and countered.
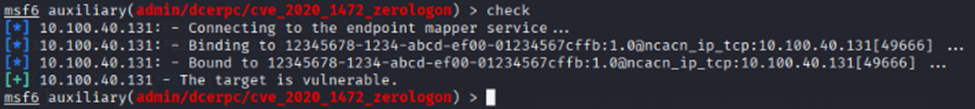
Conduct regular penetration tests: Penetration tests go way beyond a simple vulnerability scan. They involve a thorough discovery and enumeration stage and a vulnerability assessment phase, along with extensive manual testing. A penetration test is conducted with the purpose of validating whether a specific vulnerability does exist and can be exploited, while a vulnerability scan only points out that an individual vulnerability might exist. While a vulnerability scan is conducted with automated tools, such as Nessus and SAINT, a penetration test also involves an extensive manual testing stage. Manual testing allows uncovering problems that might be otherwise missed, such as input validation issues with web apps, and system and service misconfigurations in network penetration tests. By having a third-party firm conduct regular penetration tests, an organization can have an unbiased overview of its security posture, highlighting the most important problem areas regarding cybersecurity risk, the areas that could become a concern in the future, and the suitable remediation strategies that can be adopted to remediate the related risks. This allows the organization to monitor its security posture over time and to have a clearer understanding of the threat scenarios connected to its industry.
Conduct regular red teaming engagements: Red Team engagements go beyond the typical penetration test. Though penetration tests have lots of pros, they also have some cons:
They're usually pre-announced tests: The clients' security teams normally know about an upcoming engagement, so the penetration test doesn't accurately reflect how the security team would respond to a real-world attack.
IP Whitelisting: For the purposes of the test, sometimes the client might also have to whitelist a list of IP addresses belonging to the testing team. Of course, none of this would happen with real-world attackers.
Limited scope: A penetration test is conducted only against specific IP addresses/URLs that are in scope for the engagement. For example, a large global corporation could define its scope by including only its directly owned brands and excluding subsidiaries. No such artificial limitations apply to real bad guys.
Red teaming engagements (aka adversary simulations) try to mirror more closely
the TTPs (Tactics, Techniques and Procedures) used by real-world attackers. Red
teamers aren't given a specific scope, so they need to determine the target's IP
address space, relevant domains, and subdomains. They'll act like real attackers would, by prioritizing OSINT and passive reconnaissance tools (Shodan, Censys, Phonebook.cz, etc.) in order to define potentially vulnerable targets that might lead to breaching the external network to reach the internal network.
The logic behind a red teaming engagement is very different from a penetration
test. A penetration test's purpose is to identify and validate vulnerabilities
that can be exploited and provide remediation recommendations to help the organization reduce its overall risk level. Instead, a red teaming engagement aims at finding exploits or misconfigurations allowing attackers to breach the internal network and move laterally until it's completely compromised.
Additionally, red teaming engagements are conducted prioritizing stealthy attack techniques, to prevent detection. These engagements are usually only known to the client's top management. None of these considerations is present in a penetration test, as detection does not constitute a problem in that case. Red teaming engagements involve elements not always included in scope for a penetration test, such as social engineering, phishing, physical security assessments, social media monitoring, search for compromised credentials on the dark or clear web, etc.
Therefore, red teaming engagements can provide more realistic indications about an organization's security posture, along with the velocity and effectiveness of its response to an attack. However, they can be more expensive and time-consuming than normal penetration tests, because they're much more complex and require a longer period of time to be completed.
Wrap Up
The recent developments of the situation in Ukraine led to new threat scenarios of modern warfare that pose an unprecedented threat to governments and organizations.
These threats can be, however, handled and reduced by following 5 best practices:
Asset inventory management program
Vulnerability management and patch management program
Network segmentation
Regular penetration tests
Regular red teaming engagements

Polito Inc. offers a wide range of security consulting services including threat hunting, penetration testing, vulnerability assessments, red teaming engagements, incident response, digital forensics, and more. If your business or your clients have any cyber security needs, contact our experts and experience what Masterful Cyber Security is all about.
Phone: 571-969-7039
E-mail: info@politoinc.com
Website: politoinc.com



Comments